Published
- 8 min read
SPIFFE and SPIRE : Benefits, Examples, and Use Cases (Part 2)
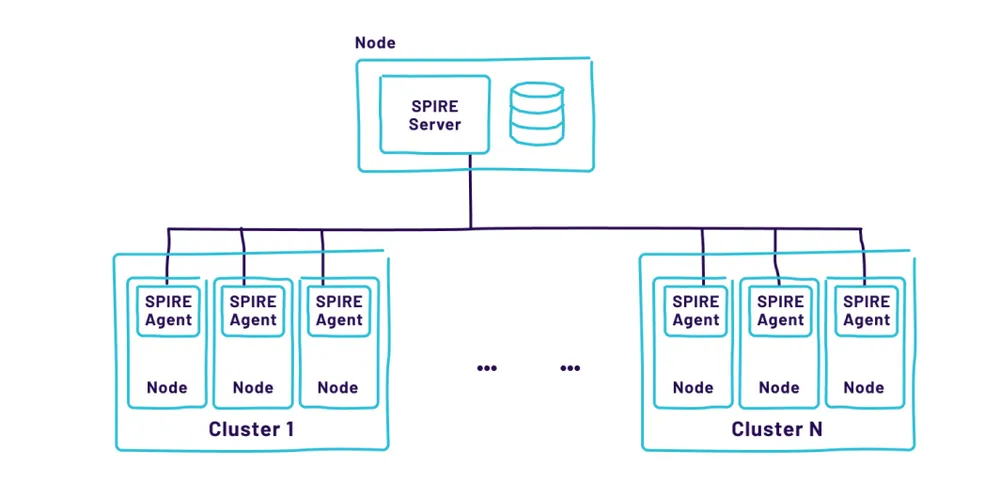
In Part 1, we established that SPIFFE is the standard for machine identity, and SPIRE is the engine that issues these identities based on verified properties rather than shared secrets.
But a question remains for many security architects: “Why do I need this? I already have AWS IAM, Azure Entra ID, and HashiCorp Vault. Isn’t that enough?”
The answer lies in the limitations of those tools when you step outside their specific walled gardens. Traditional IAM is designed for humans or single-cloud environments. SPIFFE is designed for software running anywhere.
In this second installment, we move from theory to practice. We will dismantle the differences between SPIFFE and classic IAM, explore the specific use cases where SPIRE shines, and examine how industry giants like Uber, Netflix, and ByteDance use this technology to secure their massive infrastructure.
1. SPIFFE/SPIRE vs. Traditional IAM: The Paradigm Shift
To understand the value of SPIRE, we must look at where traditional Identity and Access Management (IAM) falls short in a cloud-native world.
The “Silo” Problem
Cloud Provider IAM (like AWS IAM roles) is fantastic as long as you stay 100% within that cloud.
- The Issue: If you have an on-premise application that needs to talk to an S3 bucket, or a service in Google Cloud that needs to query an Azure SQL database, IAM becomes a headache. You usually resort to generating long-lived static keys (Access Keys) and burying them in the foreign environment.
- The SPIFFE Fix: SPIFFE is vendor-neutral. A workload on-premise can present a SPIFFE ID that AWS trusts via OIDC Federation. No long-lived keys are ever created or transferred. The identity travels with the workload, regardless of the infrastructure.
The “Granularity” Problem
Traditional network security relies on IP addresses, and traditional secrets management relies on shared API keys.
- The Issue: IP addresses in Kubernetes are ephemeral; they change every time a Pod restarts. API keys are shared; if
Service-Ahas an API key, and that key is leaked, you don’t know which instance ofService-A(or if an attacker) is using it. - The SPIFFE Fix: SPIRE issues a unique, short-lived X.509 certificate to each instance of a workload. You can cryptographically prove not just that “Service A” is calling, but specifically “Service A, running on Node 4, in the Production Namespace.”
Summary Comparison
| Feature | Traditional IAM / Secrets | SPIFFE / SPIRE |
|---|---|---|
| Trust Basis | What you know (Password/Key) | What you are (Attested Properties) |
| Credential Lifespan | Long-lived (Months/Years) | Short-lived (Minutes/Hours) |
| Rotation | Manual or complex automation | Automatic, transparent to the app |
| Scope | Cloud/Platform specific (Siloed) | Platform Agnostic (Universal) |
| Interoperability | Low (Difficult to federate) | High (Standardized Federation) |
2. Top Use Cases: Solving Hard Problems
Where should you actually deploy SPIRE? Here are the three most common scenarios where it provides immediate ROI.
Use Case A: Hybrid/Multi-Cloud
Most enterprises are hybrid. You have legacy monoliths in a data center and microservices in the cloud.
- The Challenge: Establishing mutual trust between a bare-metal server in a data center and a Docker container in the cloud usually involves a VPN and managing static certificates manually.
- The SPIRE Solution: You run a SPIRE Server in the cloud and one on-prem. Through SPIFFE Federation, these two servers exchange trust bundles (public keys). Now, a workload on-prem can present its SVID to a cloud workload, and they can establish a secure mTLS connection. It flattens the network identity barrier.
Use Case B: Passwordless / APIKeyLess Service Authentication
Databases are the most common source of leaked credentials.
- The Challenge: Developers hardcode database passwords in config files or environment variables.
- The SPIRE Solution: Modern databases (PostgreSQL, MySQL, MongoDB) support x.509 certificate authentication.
- The SPIRE Agent delivers a certificate (SVID) to the application.
- A sidecar (like
spiffe-helper) rotates this certificate on the filesystem. - The application connects to the DB using the certificate instead of a password.
- Result: There is no password to steal. Even if an attacker steals the certificate, it expires in 5 minutes.
Use Case C: Service Mesh without the Bloat
Service Meshes like Istio use Envoy proxies to handle mTLS.
- The Challenge: Istio can be heavy and complex to manage. Sometimes you just want secure communication without the full mesh networking stack.
- The SPIRE Solution: SPIRE provides the “Identity Control Plane.” You can use SPIRE libraries in your code (e.g., Go-SPIFFE) to establish mTLS directly between services. You get the encryption and authentication benefits of a Service Mesh without the operational overhead of sidecar proxies.
3. Real-World Implementations: Lessons from the Giants
This isn’t theoretical technology. It is the backbone of some of the world’s largest platforms. Based on industry reports (including the attached resources), here is how they do it.
UBER: Identity at Scale
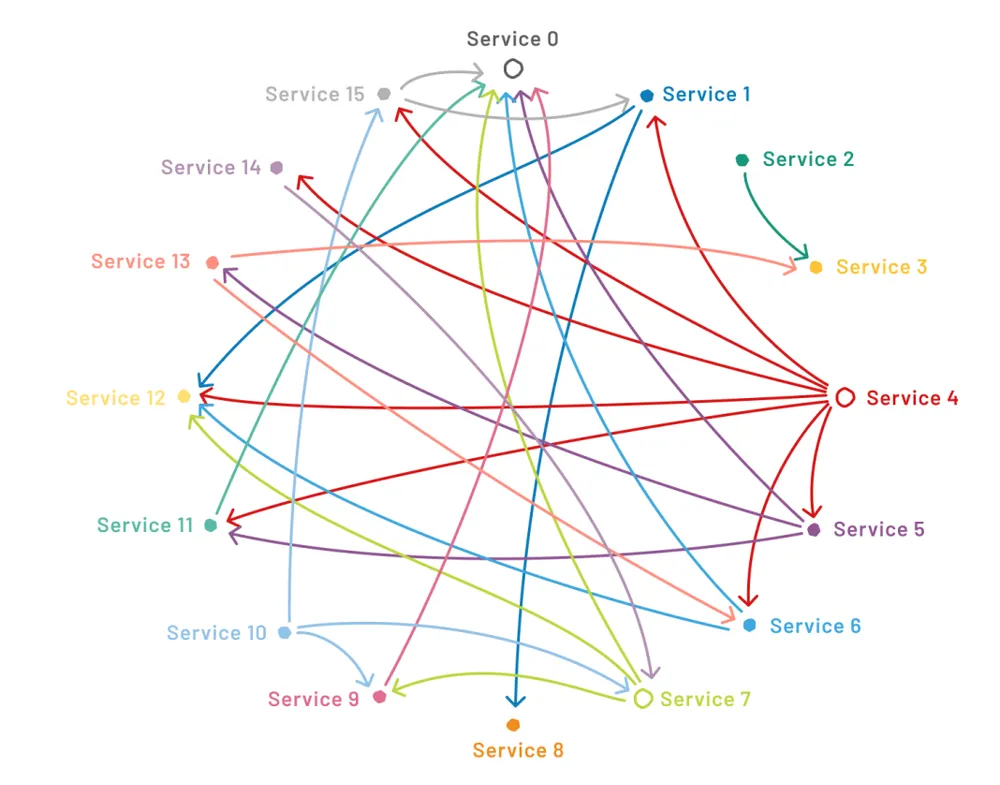
Uber runs thousands of microservices across a massive fleet of over 250,000 nodes, spanning multiple clouds and data centers.
- The Problem: They needed to guarantee that a workload running in AWS was the same identity as one running in their data center. They couldn’t rely on cloud-native IAM because they operate across four different cloud providers.
- The Implementation: Uber deployed SPIRE to create a unified “Production Trust Domain.”
- Key Innovation: They utilized Node Aliasing. By mapping physical hosts to logical groups, they could register workloads based on the “Group” they run on, rather than individual machine IDs. This allowed them to manage identity for stateless microservices and stateful storage clusters using the same pipeline.
- The Win: They achieved automated credential rotation across a heterogeneous fleet, reducing the operational burden of managing certificates to near zero.
NETFLIX: Granular Access Control
Netflix moved from a perimeter-based security model to a Zero Trust model.
- The Problem: In a massive microservices architecture, how do you prevent lateral movement if one service is compromised?
- The Implementation: They integrated SPIFFE SVIDs into their IPC (Inter-Process Communication) layer. Every request between services carries an SVID.
- The Win: Netflix reported a signficant reduction in security incidents related to credential theft. By using short-lived credentials, the window of opportunity for an attacker using stolen keys was virtually eliminated.
BYTE DANCE: Content Delivery Security
The parent company of TikTok integrated SPIFFE/SPIRE into their content delivery infrastructure.
- The Context: They have massive data flows handling content creation, moderation, and distribution.
- The Implementation: They used SPIRE to secure the communication between the microservices responsible for handling user content.
- The Win: Enhanced data privacy and compliance. By ensuring strict cryptographic identity for every service touching user data, they could enforce strict authorization policies that auditors could verify.
4. When Should You Adopt SPIFFE/SPIRE?
SPIRE is powerful, but it introduces a new infrastructure component to manage. It is not for everyone.
✅ Adopt if:
- You are Multi-Cloud/Hybrid: You need a single identity standard that works across AWS, Azure, GCP, and On-Prem.
- You have High Compliance Requirements: You need to prove exactly which process accessed data (auditing) and ensure keys are rotated frequently (e.g., every hour).
- You use Microservices/Kubernetes: You have a dynamic environment where IP-based allowlisting is becoming unmanageable.
- You want to eliminate API Keys: You are tired of key rotation headaches and finding credentials in Git repositories.
❌ Pause if:
- You have a small Monolith: If you have one big server and a database, SPIRE is over-engineering.
- Your Team is Small: Running a highly available SPIRE Server architecture requires some operational maturity.
Conclusion: The Backbone of Modern Security
SPIFFE and SPIRE are more than just tools; they represent a maturation of cloud security. We are moving away from the era of “Human-managed Secrets” to the era of “Machine-managed Identity.”
By adopting this framework, organizations like Uber and Netflix didn’t just improve security; they unlocked operational speed. Developers stopped worrying about certificate rotation and API keys, and Security teams gained sleep knowing that access is verified, encrypted, and ephemeral.
But the story doesn’t end with standard microservices. There is a new, emerging frontier where identity is even more critical: AI Agents.
In the final part of this series, we will explore the cutting edge: How SPIFFE and SPIRE are essential for securing Agentic AI, solving the unique challenges of non-deterministic, autonomous AI workloads.
To further enhance your cloud security and implement Zero Trust, contact me on LinkedIn Profile or [email protected]
Previous: ← Read Part 1: Foundations | Next: Read Part 3: AI Agent Security →
Frequently Asked Questions (FAQ)
Why use SPIRE instead of AWS IAM?
AWS IAM works perfectly within AWS, but struggles in hybrid or multi-cloud environments. SPIRE provides a unified, platform-agnostic identity layer that works across AWS, GCP, Azure, and on-premise data centers simultaneously.
Can SPIRE replace HashiCorp Vault?
Not entirely. Vault is a secrets manager (storing passwords, keys). SPIRE is an identity provider (issuing certificates). However, SPIRE can often replace the *need* for stored secrets by enabling passwordless authentication via mTLS.
Is SPIRE difficult to maintain?
It does require operational effort to set up the SPIRE Server and Agents. However, once running, it automates the massive burden of credential rotation and certificate management, often resulting in a net reduction of operational toil.
What databases support SPIFFE/SPIRE?
Any database that supports X.509 certificate authentication can work with SPIRE. This includes PostgreSQL, MySQL, MongoDB, CockroachDB, and many others.
How did Uber use SPIRE?
Uber used SPIRE to create a unified production trust domain across hundreds of thousands of nodes in multiple clouds, using features like Node Aliasing to manage identity at a massive scale.
