
For years, defenders have been playing a dangerous game of catch-up in the Software Development Life Cycle (SDLC).
The past year alone has seen a relentless barrage of attacks from the Ultralytics hijack and the devastating Shai-Hulud waves, to the TrustWallet compromise and the CodeBreach misconfiguration. Attackers have realized a simple truth: the Return on Investment (ROI) is much higher when you target the factory that builds the code, rather than hunting for vulnerabilities in the code itself.
While we have incredibly robust frameworks for protecting endpoints and cloud environments (most notably MITRE ATT&CK), securing the infrastructure that actually builds our software has largely been a “choose your own adventure” exercise.
Until now.
To bring order to the chaos of supply chain security, Wiz has introduced the SITF: SDLC Infrastructure Threat Framework.
Here is a deep dive into what SITF is, how it works, and how you can use it today to secure your engineering pipelines.
What to Remember
- Purpose-Built for SDLC: SITF maps threats specifically across the software supply chain (Endpoint, VCS, CI/CD, Registry, Production).
- Visualizes Attack Paths: The Attack Flow Visualizer helps teams understand how attackers pivot between different infrastructure components.
- Actionable Remediation: SITF links specific attack techniques to the underlying risks and the necessary preventative controls.
- Open Source & Secure: The tool runs entirely client-side in your browser, ensuring your threat models remain private.
What is SITF?
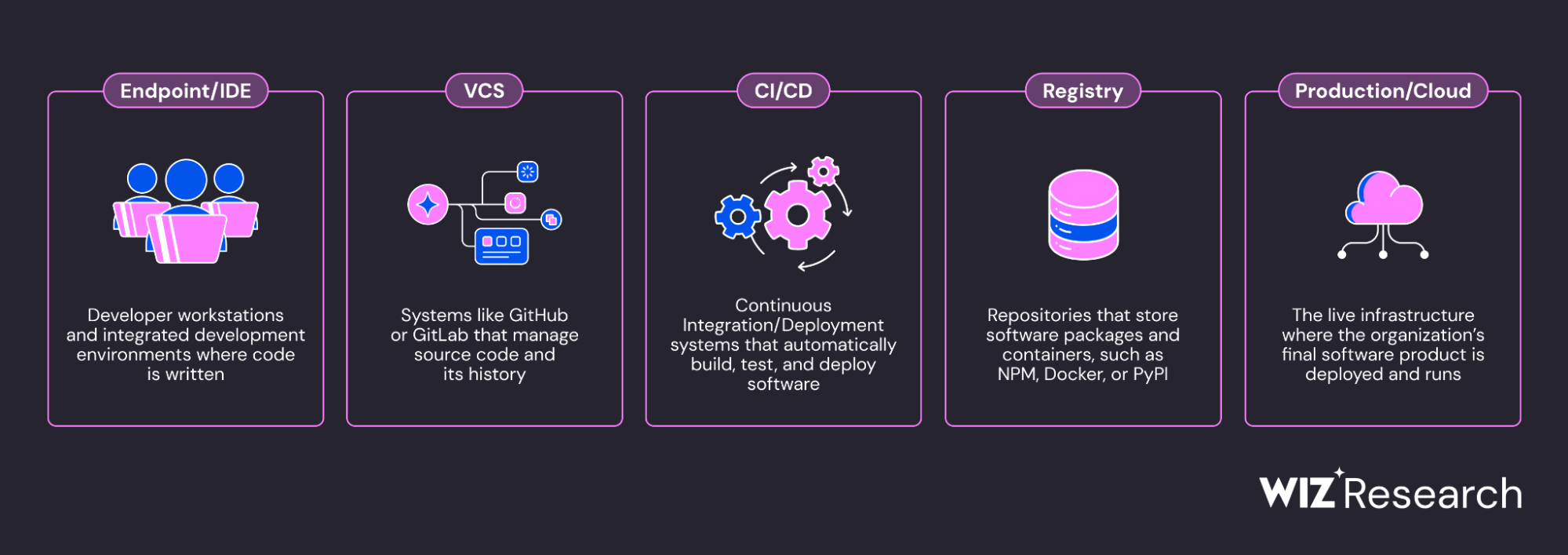
SITF is an open-source framework designed specifically to protect the “producers” the organizations creating software. It maps attacks across the five pillars of your SDLC infrastructure:
- Endpoint / IDE (Where code is written)
- VCS (Version Control Systems like GitHub/GitLab)
- CI/CD (Build pipelines and runners)
- Registry (Where packages and images are stored)
- Production (Where the software runs)
SITF distinguishes itself from existing methodologies through three core concepts:
1. Attack Flow Visualization
Supply chain attacks are rarely isolated to a single system. The recent Shai-Hulud 2.0 campaign demonstrated how an attacker can pivot from a Producer’s CI/CD, to a Registry, and finally to a Consumer’s Endpoint.
To understand these paths, SITF introduces the Attack Flow Visualizer an interactive, drag-and-drop tool that lets you map complex attack chains. It allows security teams to draw the exact vectors between an entry point (like a phishing email) and an exit point (like a secondary supply chain attack).
2. A Library of 70+ Specialized Techniques
SITF catalogs over 70 specific attack techniques unique to SDLC infrastructure. These range from “Imposter Commits” in your VCS to “Action Cache Poisoning” in your CI/CD Pipelines.
Every technique in the library is accompanied by its associated risks and necessary controls. Once you identify a threat, you immediately have an encompassing list of controls to prevent the next incident.
3. Causal Decomposition: Risk -> Technique -> Control
SITF moves beyond merely listing attacks; it decomposes every event into a causal chain.
- Technique (The “What”): e.g., T-C003: PWN Request.
- Risk (The “Why”): e.g., “Allowing PRs from forks” or “Workflows with access to secrets”.
- Control (The “Fix”): e.g., “Require explicit approval for workflows from forks”.
By mapping these relationships, SITF allows defenders to move from simply detecting a technique to mitigating the root cause risk.
Why Existing Frameworks Fall Short
We didn’t build SITF in a vacuum. It was born out of necessity following an unprecedented escalation in attacks targeting SDLC infrastructure. When security teams attempted to model these attacks, they found that existing frameworks weren’t built for this specific problem set:
- MITRE ATT&CK: The industry standard for enterprise security, but it lacks a dedicated matrix for SDLC infrastructure and focuses primarily on detecting techniques rather than preventing them.
- OWASP CI/CD Top 10: Excellent for prioritizing risks, but it lacks the architectural context and temporal flow to show how a vulnerability in a developer’s IDE leads to a compromise in Production.
- SLSA / NIST SSDF: These provide vital pieces of the puzzle (integrity and process), but miss the comprehensive, infrastructure-centric view needed for modern threat modeling.
We needed a framework that was prescriptive, actionable, and visual. We needed to answer not just “what are the risks?” but “how does an attacker move through my system?”
See It in Action: Deconstructing Shai-Hulud 2.0
To prove the framework’s utility, the Wiz team modeled the sophisticated Shai-Hulud 2.0 attack. This campaign was a sequence of distinct steps spanning VCS, CI/CD, Registry, and Endpoints.
Using SITF, the initial breach is decomposed as follows:
- The Technique (T-C003: PWN Request): The attacker submitted a malicious Pull Request from a fork, automatically triggering a CI/CD workflow.
- The Enabling Risks: The repository was configured to “Allow PRs from forks” to trigger pipelines, and the workflow had “Access to secrets.”
- The Missing Controls: To stop this, the organization needed “Branch Protection Rules” or to “Require explicit approval for PRs from forks” at the VCS level.
Once initial access was achieved, the attack accelerated through the SDLC:
- Step 2 (T-C005): Secret Exfiltration from Workflow (Stealing NPM tokens).
- Step 3 (T-R004): Publishing Malicious Package to the public registry.
- Step 4 (T-E001): Malicious Execution on Endpoint (Developers installing the poisoned package).
- Step 5 (T-E003): Harvest Local Secrets (Scraping credentials via
trufflehog).
The Payoff: The Controls Matrix
Once you’ve mapped an incident in the Visualizer, SITF automatically generates a Controls Matrix. Because the most efficient way to stop a supply chain attack is to break the chain as early as possible, the matrix is prioritized by Attack Stage (Initial Access controls rank above Post-Compromise controls) and separated by architectural component.
Get Started with SITF Today
SITF is open-source, client-side, and available now. There is no installation script, no signup, and no data ever leaves your machine.
- Access Online:Wiz SITF GitHub Pages
- Access Locally: Clone the SITF GitHub Repo and open the HTML files in your browser.
Use the Visualizer to start dragging and dropping threat models, and explore the Technique Library to audit your current infrastructure.
Because the entire framework is driven by a machine-readable JSON source of truth, you can easily modify techniques.json to fit your unique environment, or contribute new attacks and controls back to the community via Pull Requests.
The software supply chain is under attack. It is time we mapped the battlefield.
To further enhance your cloud security and secure your SDLC, contact me on LinkedIn Profile or [email protected].
Frequently Asked Questions (FAQ)
What is SITF?
SITF (SDLC Infrastructure Threat Framework) is an open-source framework by Wiz designed to visualize, analyze, and prevent complex software supply chain attacks across five pillars: Endpoint/IDE, VCS, CI/CD, Registry, and Production.
How does SITF differ from MITRE ATT&CK?
While MITRE ATT&CK is the industry standard for enterprise security and focuses on detecting techniques, SITF is specifically tailored for SDLC infrastructure, focusing on the causal chain of Risk -> Technique -> Control to prevent supply chain attacks.
What is the Attack Flow Visualizer?
The Attack Flow Visualizer is an interactive, drag-and-drop tool within SITF that allows security teams to map complex attack chains, showing exactly how an attacker moves between different stages of the SDLC (e.g., from a phishing email to a compromised registry).
How does SITF use Causal Decomposition?
SITF breaks down every event into a causal chain: the Technique (the attack method), the Risk (the vulnerability or misconfiguration enabling it), and the Control (the security measure to fix it). This helps defenders mitigate root causes rather than just detecting attacks.
Is SITF free and secure to use?
Yes, SITF is open-source and runs entirely client-side in your browser. No installation is required, and no data ever leaves your machine. You can access it via GitHub Pages or clone the repository to run it locally.
Resources
- Wiz SITF GitHub Pages: https://wiz-sec-public.github.io/SITF/
- SITF GitHub Repo:https://github.com/wiz-sec-public/SITF
- MITRE ATT&CK Framework:https://attack.mitre.org/
- OWASP CI/CD Top 10: https://owasp.org/www-project-top-10-ci-cd-security-risks/
