Published
- 9 min read
The Quantum-Proof Handshake: Your Blueprint for Migrating to Post-Quantum TLS

For years, the padlock icon in our browsers powered by TLS has symbolized secure online communication, protecting everything from shopping to cloud services. But the rise of quantum computing threatens to break the encryption methods TLS relies on.
Quantum computers could soon crack the cryptographic algorithms we use today, putting long-term data security at risk. To stay ahead, we must move toward Post-Quantum TLS. This migration is particularly critical for organizations implementing modern cloud security strategies.
This guide will help you understand the threat, explore the solution, and take practical steps to prepare for the future of encryption.
The Looming Threat: “Harvest Now, Decrypt Later”
The most urgent problem posed by quantum computing isn’t that an attacker will break your live TLS session tomorrow. It’s the insidious strategy known as “Harvest Now, Decrypt Later.”
Here’s the scenario: an adversary intercepts and records vast amounts of your encrypted network traffic today. This could be anything from sensitive customer data and intellectual property to financial transactions and confidential communications. While this data is perfectly secure against today’s classical computers, it is stored away in data vaults, waiting. The moment a cryptographically relevant quantum computer (CRQC) becomes operational, this trove of harvested data can be retrospectively decrypted, exposing years of secrets.
The core vulnerability lies in the key exchange phase of the TLS handshake. This is the moment when the client and server use asymmetric cryptography (like RSA or ECC) to securely agree upon a symmetric key for the session. It is precisely this public-key cryptography that is susceptible to Shor’s algorithm, the quantum algorithm that will render it obsolete. Every TLS session protected by these classical algorithms is a potential target for this long-term data harvesting.
The Solution: Weaving PQC into the TLS Handshake
The answer to the quantum threat is Post-Quantum Cryptography (PQC), a new generation of cryptographic algorithms designed to be resistant to attack by both classical and quantum computers. The global standardization effort, led by the U.S. National Institute of Standards and Technology (NIST), has identified several promising algorithms, with Kyber (ML-KEM) emerging as the primary standard for key exchange.
But how do we integrate these new, and in some cases less battle-tested, algorithms into a protocol as critical as TLS without breaking the internet or introducing new risks? The answer is a clever and resilient strategy: the hybrid key exchange.
The Hybrid Key Exchange: The Best of Both Worlds
A hybrid approach doesn’t force a sudden, risky switch to PQC. Instead, it combines a classical key exchange algorithm with a post-quantum one.
Here’s how it works within a TLS 1.3 handshake:
- Client Hello: The client (e.g., your browser) initiates the handshake by sending a
ClientHellomessage. Instead of offering just one key share (e.g., for ECDH), it sends two key shares: one for the classical algorithm (e.g., x25519) and one for the PQC algorithm (e.g., kyber-768). - Server Hello: The server, if it supports this hybrid approach, processes both key shares. It generates its own corresponding key pairs and sends back its public keys in the
ServerHellomessage. - Shared Secret Generation: Both the client and the server now independently use both sets of keys to derive two separate shared secrets. These two secrets are then cryptographically combined to generate the final, single session key that will be used to encrypt all traffic for the remainder of the session.
This hybrid model is ingeniously resilient.
- If the PQC algorithm is one day found to have a weakness against a classical computer, the session remains secure because it’s still protected by the proven strength of ECDH.
- If a quantum computer comes online and breaks ECDH, the session remains secure because it’s protected by the quantum-resistant PQC algorithm.
An attacker would need to break both the classical and the post-quantum algorithms to compromise the session, providing a robust, defense-in-depth approach for this transitional era. This approach aligns with modern cloud threat detection principles.
Real-World Implementation: The Practical Hurdles and Considerations
Migrating to Post-Quantum TLS is not as simple as flipping a switch. It requires careful planning and consideration of the real-world impacts on your infrastructure and applications.
1. The Critical Role of TLS 1.3
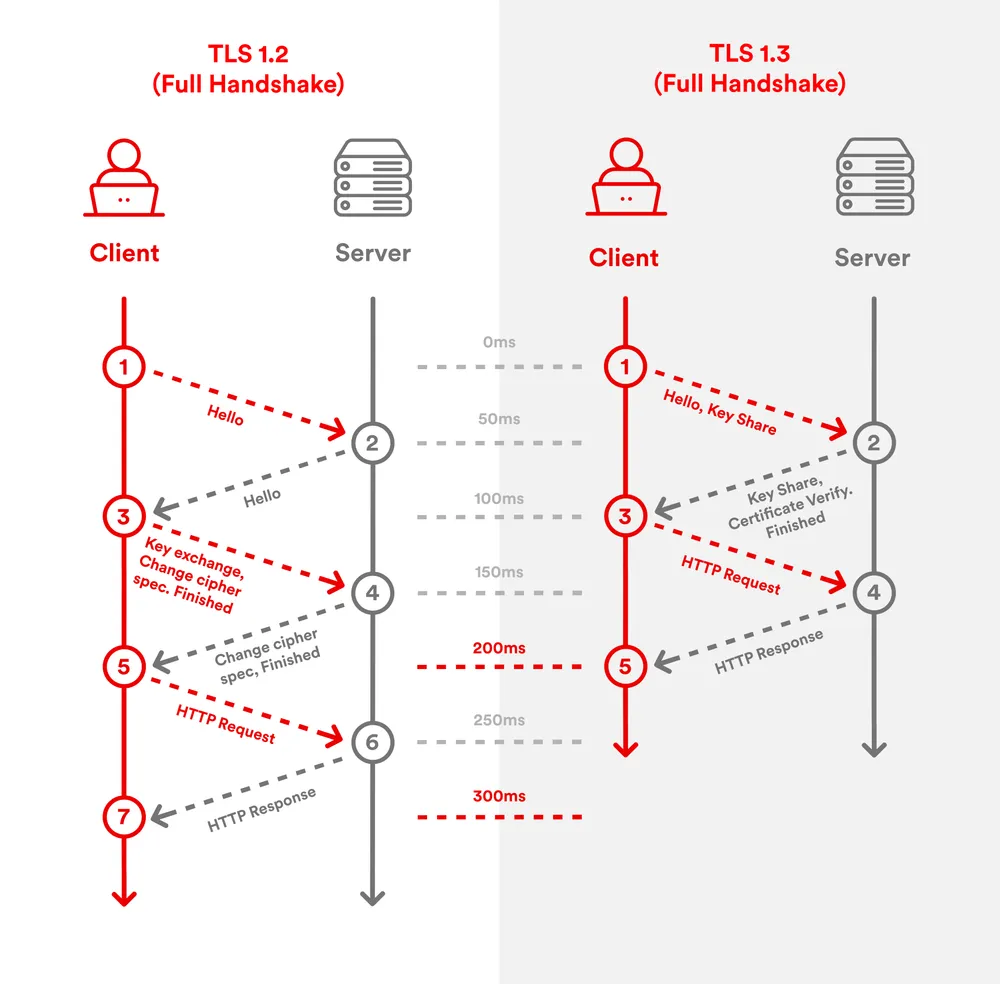
The hybrid key exchange model is designed for and works most seamlessly with TLS 1.3. The protocol was designed with cryptographic agility in mind, making it far easier to extend and incorporate new key exchange mechanisms. While it might be technically possible to backport hybrid approaches to TLS 1.2, it is far more complex and not the recommended path. This makes upgrading your entire infrastructure to be TLS 1.3-native a foundational “no-regrets” move in your PQC journey.
2. The Performance Impact: Latency and Bandwidth
There is no such thing as a free lunch in cryptography. PQC algorithms come with trade-offs.
- Larger Key Sizes: Post-quantum key shares are significantly larger than their classical counterparts. This means the
ClientHelloandServerHellomessages will be bigger, consuming more bandwidth. - Increased Computational Cost: The cryptographic operations for PQC can be more computationally intensive, potentially increasing CPU load on servers and affecting the speed of the handshake.
- Potential for Extra Round Trips: Some hybrid implementations might require an extra round trip during the handshake, which can significantly impact latency, especially for users on high-latency networks.
These performance impacts must be carefully tested and measured in a controlled environment to understand their effect on your specific applications and user experience.
3. Crypto-Agility: Designing for a Fluid Future
The PQC landscape is still maturing. While NIST has selected its initial standards, new algorithms and new attacks will inevitably emerge. The most important strategic capability an organization can build is crypto-agility. This means architecting your systems in a way that allows you to easily and rapidly swap out cryptographic algorithms without requiring a massive overhaul. Hardcoding cryptographic libraries or protocols is a recipe for future pain.
4. Ecosystem Readiness
A TLS handshake is a dance between two partners. Your PQC migration is dependent on the entire ecosystem being ready. This includes:
- Client-side support (browsers, mobile applications, IoT devices).
- Server-side support (web servers, load balancers, API gateways).
- Underlying libraries (like OpenSSL or BoringSSL).
- Hardware Security Modules (HSMs) and other specialized hardware.
A CISO’s Action Plan for Post-Quantum TLS
The transition to PQC is a marathon, not a sprint, but the starting gun has already fired. Here are five actionable steps every CISO should be taking now:
- Create a Cryptographic Inventory. You cannot protect what you do not know you have. The first step is to create a comprehensive inventory of all cryptographic systems, libraries, and dependencies used across your organization. Identify every application and system that relies on TLS and what algorithms it is currently using.
- Prioritize Critical Data Flows. Not all TLS sessions are created equal. Analyze your data flows and prioritize the migration for those that carry your most sensitive, long-lived data the prime targets for “Harvest Now, Decrypt Later” attacks.
- Mandate the Upgrade to TLS 1.3. Make migrating all your systems to support TLS 1.3 a top priority. This is a crucial prerequisite for a smooth PQC transition and offers significant security and performance benefits on its own.
- Engage Your Vendors. Start the conversation with all your key technology vendors. What is their PQC roadmap? When will their products support hybrid key exchange? Their timelines will be a critical input into your own migration plan.
- Begin Testing and Proofs of Concept (PoCs). The time to start experimenting is now. Set up a lab environment to test hybrid PQC implementations. Measure the performance impact, check for compatibility issues, and begin building the institutional knowledge required for a full-scale deployment.
Conclusion: Building the Next Generation of Trust
The silent handshake that secures our digital world is on the cusp of a profound evolution. The threat of quantum computing requires us to re-architect the very foundations of our cryptographic trust. The move to Post-Quantum TLS, powered by a resilient hybrid key exchange model, is the clear path forward.
While the journey is complex and requires careful planning, the cost of inaction is far greater. By starting today by inventorying your assets, prioritizing your most sensitive data, upgrading your infrastructure, and engaging with your partners you can ensure that your organization is not just prepared for the quantum future, but is actively building a more secure and trustworthy digital world.
To further enhance your cloud security and implement Zero Trust, contact me on LinkedIn Profile or [email protected].
Frequently Asked Questions (FAQ)
What is Post-Quantum Cryptography (PQC)?
PQC refers to a new generation of public-key cryptographic algorithms that are designed to be secure against attacks from both today's classical computers and future quantum computers.
Why is TLS vulnerable to quantum computers?
The key exchange phase of TLS versions 1.2 and earlier, and the standard configuration of 1.3 relies on algorithms like RSA and ECDH. A sufficiently powerful quantum computer running Shor's algorithm will be able to break the underlying mathematics of these algorithms, allowing an attacker to decrypt captured sessions.
What is a hybrid key exchange?
A hybrid key exchange combines a classical algorithm like ECDH and a post-quantum algorithm like Kyber within a single TLS handshake. The final session key is derived from both, ensuring the connection is secure as long as at least one of the algorithms remains unbroken.
Do I need to upgrade to TLS 1.3 to use PQC?
While not strictly impossible to implement in older versions, TLS 1.3's modern and extensible design makes it the ideal and strongly recommended protocol for deploying hybrid PQC. Upgrading to TLS 1.3 is a critical first step.
When do I need to complete my migration to Post-Quantum TLS?
The threat is now, due to "Harvest Now, Decrypt Later" attacks on data that must remain confidential for many years. The migration itself is a multi-year journey. The consensus is that organizations, especially those with sensitive, long-lived data, must start the planning and inventory process immediately.
Relevant Resource List
- Akamai Blog: “Post-Quantum Cryptography Implementation Considerations for TLS”
- NIST Post-Quantum Cryptography Project: The official source for PQC standardization efforts.
- IETF (Internet Engineering Task Force): For draft standards and technical specifications related to PQC in TLS and other protocols.
- Cloudflare Blog: A key industry player often publishing deep dives and performance analysis of PQC implementations.
- Google Security Blog: For information on Chrome’s PQC experiments and the “CECPQ2” hybrid key exchange.
